Keep your crypts on exchange: Basic good procedures
Maintaining crypts on the centralized Stock Exchange (CEX) has specific risks: hacks, bankruptcies, downloads, human mistakes. However, if you are acting active trading or using specific features, you will ever have to keep the funds on the platform. In this case, use the following good procedures to clearly strengthen the security level.
If you really need to maintain cryptocurrencies on a platform such as binance or coinbase rather than your wallet (wallet), here are our recommendations so that we can protect you at best other risks 👇
Activate double verification (2FA)
Double verification adds another barrier to access your account: After the password, you must connect with a single use code from a dedicated application on your phone or using a physical security key.
This additional step makes all the differences, because even if someone knows your password, so you won’t be able to connect to your account if you don’t have access to your smartphone. This system makes your account extremely complex.
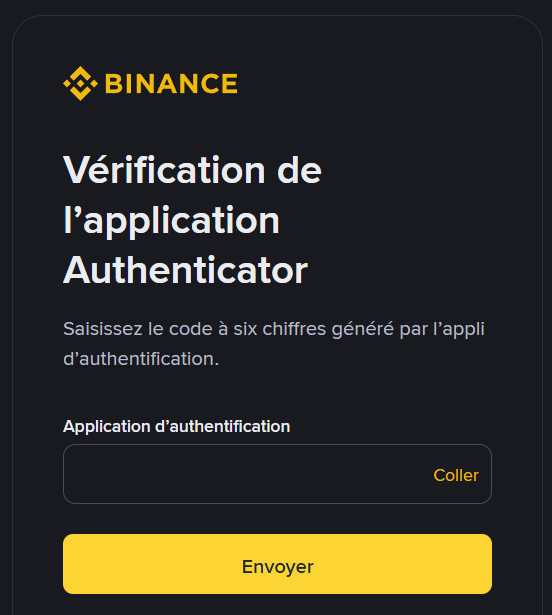
Example Binance connection when 2FA is activated
Absolutely avoid verifying by SMS that can be diverted using SIM exchange attacks, where the attacker takes control of your number, prefer a verification application installed on your smartphone, such as Google Authenticator or Authy.
Also, be sure to save your backup codes to check that double verification for sensitive actions such as selections or API keys is also activated.
💡 Here is our guide dedicated to the implementation of double verification (2FA)
Configure the sentence against phishing
The phishing sentence is a short and personalized text that you define in the Safety Settings settings. When it sends you a legitimate e -mail, the platform displays this sentence in the message. It is a visual benchmark that will help you distinguish the real e -mail from the platform from an attempt at usurpation that mimics its identity.
This is essential because phishing remains the first front door of the attackers. Without a reliable benchmark, e -mail can mimic the Charter Charter by clicking on the captured link or entering your identifiers on a fake page.
The anti phishing sentence complicates this fraud: if it does not seem or is not exactly the one you have chosen, consider it an attempt at phishing.
Protect yourself from phishing with nordvpn
Advertisement
Leave only the strict needed to exchange
Replacement is not safe, it is a tool to make orders with your cryptocurrencies.
Keep only capital useful for your short -term trading and regularly reatter the surplus to your personal wallet

Different models of crypto wallet offered Ledger
Secure your crypts using a nano wallet with a book for only 49 euros
Advertisement
Use regulated and transparent platforms
They prefer actors in France (SIDA licenses) with clear administration and history of conformity.
Also evaluate transparency: communication during incidents, security documentation, understandable conditions of use or reactive customer support.
Reserve evidence is useful to confirm the existence of cryptocurrencies, but do not replace regulation or solid internal controls.
👉 Discover a list of the best cryptomic platforms for investment in complete safety
Use the AE -Mail Passwords Reserved
When creating an account, select one password, long and difficult to guess and record it in password manager, such as NordPass rather than remember or reuse elsewhere.
Ideally, book the e -mail address designed for your crypt accounts (not a personal address) to limit the exposure in the case of another service and better filter suspicious messages.
Then secure this mailbox by double verification using the application, if possible, deactivate verification using SMS and find the recovery options.
Simplify the security of your passwords using NordPass
Advertisement
Activate the white list of addresses
Downloading the selection has limited cryptocurrency outputs only to addresses you verified.
Specifically, even if you copy the wrong address, select the wrong network or create a typo, the platform blocks the download because the address is not on the list. Indicate clear and personalized names to each address to avoid confusion.

Activate the safety period
The safety time is stored waiting time than the new download address is applicable. For 24 to 72 hours depending on your modification, any retreat from cryptocurrencies to this address is blocked, leaving you the time to respond if your account is at risk.
If the stock exchange permits, use this period to deactivate the whitelist and account protection accounts. In the case of warning during this period, freezing and canceling the API keys.
Ensure a good digital hygiene of your devices
Your digital environment will be subject to your safety. Hold the system, browser and up -to -Date applications and use the famous antivirus.
It is also recommended to reduce the browser extension to the necessary and ideally book a profile or browser dedicated to trading. Install only the official platform application from reliable sources and access to the web through your favorites, never from the link.
👉 Our complete guide ensured your digital and financial environment
Learn to detect Phishing attempts
Phishing is to push you to click on a deceptive link or understand your identifiers on a page that perfectly mimics your platform, playing in an emergency, fear or promise of exceptional benefits.
Face in the face of an alarming message that evokes a suspicious connection, unexpected refund or a limited gift in time, always insist a few seconds to check the sender, carefully read the site address and find details that betray fraud like a slightly changed area, spelling errors or approximate layout.
Never use the links contained in -mail to connect to exchange: Open your browser, click the favorite you have saved yourself, and then control your notifications directly in the official interface.
Use several platforms if necessary
Relying on one cryptological platform unnecessarily concentrates technical and operating risks: extended schedule, temporary gel withdrawal, hack or simple problem verification of identity can suffice to immobilization.
By distributing cryptos between 2 or 3 platforms, you will get durability without complicating your organization.
Let your capital grow with analyzes and strategies of our experts
Advertisement
Although it may be interesting to leave your cryptocurrencies on the stock exchange for various reasons, The best thing you need to ensure their safety is to use a crypt of wallet where you are the only master on board.
💡 Do you just want to go for a wallet? Find our 10 best best crypto portfolio, whether free or paid
Some content or links in this article may be an ad. Cryptoast studied presented products or services, but cannot be responsible for any damage or loss associated with their use. Investment in cryptocurrencies involves risks. Invest only what you are ready to lose.
Crypto newsletter n ° 1 🍞
Get a summary of crypto messages every day e -mail 👌
